Wireshark is the world's most popular network protocol analyzer — and for good reason. Whether you're troubleshooting a sluggish application, investigating a security breach, or studying for your CCNA certification, Wireshark gives you unprecedented visibility into what's happening on your network.
This comprehensive cheat sheet covers everything from basic display filters to advanced forensic analysis techniques. We've organized 200+ filters, commands, and techniques into logical sections so you can quickly find exactly what you need. Plus, you can download the complete 22-page PDF for offline reference.
📥 Free Download: Wireshark Complete Cheatsheet 2026
22 pages • 200+ filters • tshark CLI • Forensics • VoIP • Wireless
Download Free PDF →1. Display Filter Fundamentals
Display filters are the most powerful feature in Wireshark. They let you narrow down captured traffic to exactly what you need to see. Understanding the syntax is essential for efficient packet analysis.
Comparison Operators
| Operator | Example | Description |
|---|---|---|
== (eq) | ip.addr == 192.168.1.1 | Equal to |
!= (ne) | ip.addr != 10.0.0.1 | Not equal to |
> (gt) | frame.len > 1000 | Greater than |
< (lt) | tcp.port < 1024 | Less than |
contains | http.host contains "google" | Field contains value |
matches (~) | http.host matches "\.(com|org)$" | Regex match |
in | tcp.port in {80, 443, 8080} | Value in set |
Logical Operators
# AND - both conditions must match
ip.src == 10.0.0.1 && tcp.port == 80
# OR - either condition matches
dns || http
# NOT - exclude matching packets
!arp
# Grouping with parentheses
(ip.src == 10.0.0.1) && (tcp.port == 80 || tcp.port == 443)2. Capture Filters (BPF Syntax)
Capture filters use Berkeley Packet Filter (BPF) syntax — a completely different language from display filters. They're applied before packets are captured, which is critical for high-traffic networks where you'd otherwise run out of memory.
Essential Capture Filters
| Filter | Description |
|---|---|
host 192.168.1.1 | Traffic to/from specific host |
net 192.168.1.0/24 | Traffic for entire subnet |
port 80 | Traffic on specific port |
tcp | TCP traffic only |
not broadcast | Exclude broadcast traffic |
host 10.0.0.1 and port 443 | HTTPS to specific host |
not port 22 | Exclude SSH traffic |
icmp | ICMP traffic only (ping, traceroute) |
ip.addr == 192.168.1.1 is a display filter. host 192.168.1.1 is the equivalent capture filter. Don't mix them up.
3. IP & Ethernet Filters
IP Address Filtering
# Traffic involving specific IP (source OR destination)
ip.addr == 192.168.1.1
# Source IP in private range
ip.src == 10.0.0.0/8
# Packets with low TTL (routing issues)
ip.ttl < 10
# Fragmented packets
ip.flags.mf == 1
# IPv6 traffic
ip.version == 6
# ARP requests only
arp.opcode == 1
# Duplicate IP detection
arp.duplicate-address-detected4. TCP Analysis & Troubleshooting
TCP analysis is where Wireshark truly shines. Understanding TCP flags and Wireshark's built-in analysis expert helps you quickly identify network performance problems.
TCP Flag Filters
| Filter | What It Finds |
|---|---|
tcp.flags.syn == 1 && tcp.flags.ack == 0 | Initial connection requests (SYN only) |
tcp.flags.syn == 1 && tcp.flags.ack == 1 | Server responses (SYN-ACK) |
tcp.flags.fin == 1 | Connection termination |
tcp.flags.reset == 1 | Connection resets (refused/aborted) |
TCP Troubleshooting Filters
# Retransmissions (packet loss indicator)
tcp.analysis.retransmission
# Duplicate ACKs (receiver requesting retransmission)
tcp.analysis.duplicate_ack
# Zero window (receiver buffer full)
tcp.analysis.zero_window
# Out-of-order segments
tcp.analysis.out_of_order
# Lost segments
tcp.analysis.lost_segment
# Follow a specific TCP conversation
tcp.stream eq 5
# All TCP problems combined
tcp.analysis.flagsStatistics > TCP Stream Graphs > Round Trip Time to visualize latency per stream.
5. HTTP/HTTPS Traffic Analysis

HTTP Filters
# All HTTP requests
http.request
# Specific methods
http.request.method == "GET"
http.request.method == "POST"
# API endpoint requests
http.request.uri contains "/api/"
# Specific host
http.host == "example.com"
# Error responses
http.response.code >= 400 # All errors
http.response.code == 404 # Not Found
http.response.code >= 500 # Server errors
# Content types
http.content_type contains "json"
http.content_type contains "html"
# Authentication headers
http.authorization
http.cookie contains "session"TLS/HTTPS Decryption
To decrypt HTTPS traffic in Wireshark:
- Set the
SSLKEYLOGFILEenvironment variable in your browser before capturing - In Wireshark:
Edit > Preferences > Protocols > TLS - Set the
(Pre)-Master-Secret log filenameto your key log file - Wireshark will automatically decrypt matching TLS sessions
# TLS handshake messages
tls.handshake
# Client Hello (connection initiation)
tls.handshake.type == 1
# Server Name Indication (SNI) filter
tls.handshake.extensions_server_name contains "example"
# TLS 1.3 traffic
tls.handshake.extensions.supported_versions == 0x0304
# TLS alerts (errors)
tls.alert_message6. DNS Investigation
Essential DNS Filters
| Filter | Purpose |
|---|---|
dns.qry.name == "example.com" | Queries for specific domain |
dns.flags.rcode == 3 | NXDOMAIN (domain not found) |
dns.qry.type == 1 | A record queries (IPv4) |
dns.qry.type == 28 | AAAA record queries (IPv6) |
dns.qry.type == 15 | MX record queries (mail) |
dns.qry.type == 16 | TXT record queries |
dns.count.answers > 10 | Suspiciously many answers |
dns.qry.name.len > 50 | Long domains (tunneling indicator) |
dns.qry.name.len > 50 || dns.resp.len > 512
7. tshark Command-Line Interface
tshark is the command-line version of Wireshark — essential for headless servers, scripting, and automated analysis. It supports the same display filters and protocol dissectors.
Essential tshark Commands
# List available interfaces
tshark -D
# Capture 1000 packets on eth0
tshark -i eth0 -c 1000
# Capture with display filter
tshark -i eth0 -Y "http.request"
# Write to file
tshark -i eth0 -w capture.pcapng
# Read file with filter
tshark -r capture.pcapng -Y "dns"
# Custom field output
tshark -r capture.pcapng -T fields -e ip.src -e ip.dst -e tcp.port
# JSON output
tshark -r capture.pcapng -T json -Y "http.request"
# Ring buffer (rotate 10 files, 100MB each)
tshark -i eth0 -b filesize:102400 -b files:10 -w ring.pcapng
# Extract HTTP objects
tshark -r capture.pcapng --export-objects http,./exported_files/
# Protocol hierarchy statistics
tshark -r capture.pcapng -z io,phs
# TCP conversation statistics
tshark -r capture.pcapng -z conv,tcpCompanion CLI Tools
| Tool | Purpose |
|---|---|
editcap | Split, trim, convert, and deduplicate capture files |
mergecap | Merge multiple capture files into one |
capinfos | Display capture file statistics (packets, duration, size) |
dumpcap | Low-level capture tool (used by Wireshark internally) |
text2pcap | Convert hex dump text to pcap format |
8. Network Forensics & Security

Wireshark is an indispensable tool for security investigations. Here are the key filters for detecting malicious activity.
Port Scan Detection
# TCP SYN scan (many SYN, few established connections)
tcp.flags.syn == 1 && tcp.flags.ack == 0
# NULL scan (no flags set)
tcp.flags == 0x000
# XMAS scan (FIN+PSH+URG)
tcp.flags.fin == 1 && tcp.flags.push == 1 && tcp.flags.urg == 1
# Many RST responses (closed ports)
tcp.flags.reset == 1Threat Detection Filters
| Threat | Filter |
|---|---|
| ARP Spoofing | arp.duplicate-address-detected |
| DNS Tunneling | dns.qry.name.len > 50 || dns.resp.len > 512 |
| ICMP Tunneling | icmp && data.len > 64 |
| SSH Brute Force | tcp.port == 22 && tcp.flags.syn == 1 |
| Cleartext Credentials | http.authorization || ftp.request.command == "PASS" |
| Suspicious HTTP | http.user_agent contains "curl" || http.user_agent contains "wget" |
| Data Exfiltration | tcp.len > 10000 && !(http || tls) |
| HTTP to IP (no domain) | http.host matches "^[0-9]+\.[0-9]+" |
9. VoIP & SIP/RTP Analysis
SIP Call Analysis
# All SIP traffic
sip
# Call initiation
sip.Method == "INVITE"
# Call termination
sip.Method == "BYE"
# SIP errors
sip.Status-Code >= 400
# RTP media streams
rtp
# RTCP quality reports
rtcpUse Telephony > VoIP Calls for a complete call listing with duration and codecs. Telephony > RTP Player can play back captured audio. Call quality issues show as jitter >30ms, packet loss >1%, or latency >150ms.
10. Wireless (802.11) Capture
Wireless capture requires your adapter to support monitor mode. Key filters for WiFi analysis:
# Management frames (beacons, probes, auth)
wlan.fc.type == 0
# Beacon frames
wlan.fc.type_subtype == 0x0008
# Specific SSID
wlan.ssid == "MyNetwork"
# Deauthentication frames (attack indicator!)
wlan.fc.type_subtype == 0x000c
# WPA handshake capture
eapol
# Probe requests (device discovery)
wlan.fc.type_subtype == 0x000411. Performance & Statistics
Performance Problem Filters
| Problem | Filter |
|---|---|
| TCP Retransmissions | tcp.analysis.retransmission |
| Out-of-Order Packets | tcp.analysis.out_of_order |
| Zero Window | tcp.analysis.zero_window |
| Connection Resets | tcp.flags.reset == 1 |
| Slow DNS | dns.time > 0.5 |
| Slow HTTP | http.time > 1 |
| High Latency | frame.time_delta > 0.1 |
Statistics Menu Quick Reference
- Statistics > Protocol Hierarchy — Protocol breakdown by percentage
- Statistics > Conversations — Top talkers by bytes/packets
- Statistics > Endpoints — All unique endpoints with traffic volume
- Statistics > I/O Graphs — Visual traffic over time (add custom filters)
- Statistics > Flow Graph — Sequence diagram between hosts
12. Keyboard Shortcuts
| Shortcut | Action |
|---|---|
| Ctrl+E | Start/Stop capture |
| Ctrl+R | Restart capture |
| Ctrl+F | Find packet |
| Ctrl+G | Go to packet number |
| Ctrl+M | Mark/Unmark packet |
| Ctrl+T | Set time reference |
| Ctrl+Shift+S | Save capture as... |
| Right-click > Follow | Follow TCP/UDP/HTTP stream |
Top 15 Must-Know Filters
If you remember nothing else from this cheat sheet, memorize these 15 filters. They'll solve 90% of your network analysis needs:
ip.addr == x.x.x.x # Traffic involving specific IP
tcp.port == 80 # HTTP port traffic
dns # All DNS traffic
http.request # HTTP requests only
tcp.flags.syn == 1 # Connection initiations
tcp.flags.reset == 1 # Connection resets
tcp.analysis.retransmission # Retransmitted packets
!arp && !dns # Exclude ARP and DNS noise
tcp.stream eq N # Follow specific TCP stream
http.response.code >= 400 # HTTP errors
tls.handshake # TLS handshakes
frame.len > 1000 # Large packets only
tcp.analysis.zero_window # Zero window events
dns.flags.rcode != 0 # DNS errors
tcp.analysis.flags # All TCP problems📥 Download the Complete Wireshark Cheatsheet
22 pages of filters, commands, and techniques — free PDF download
Download Free PDF →Related Resources
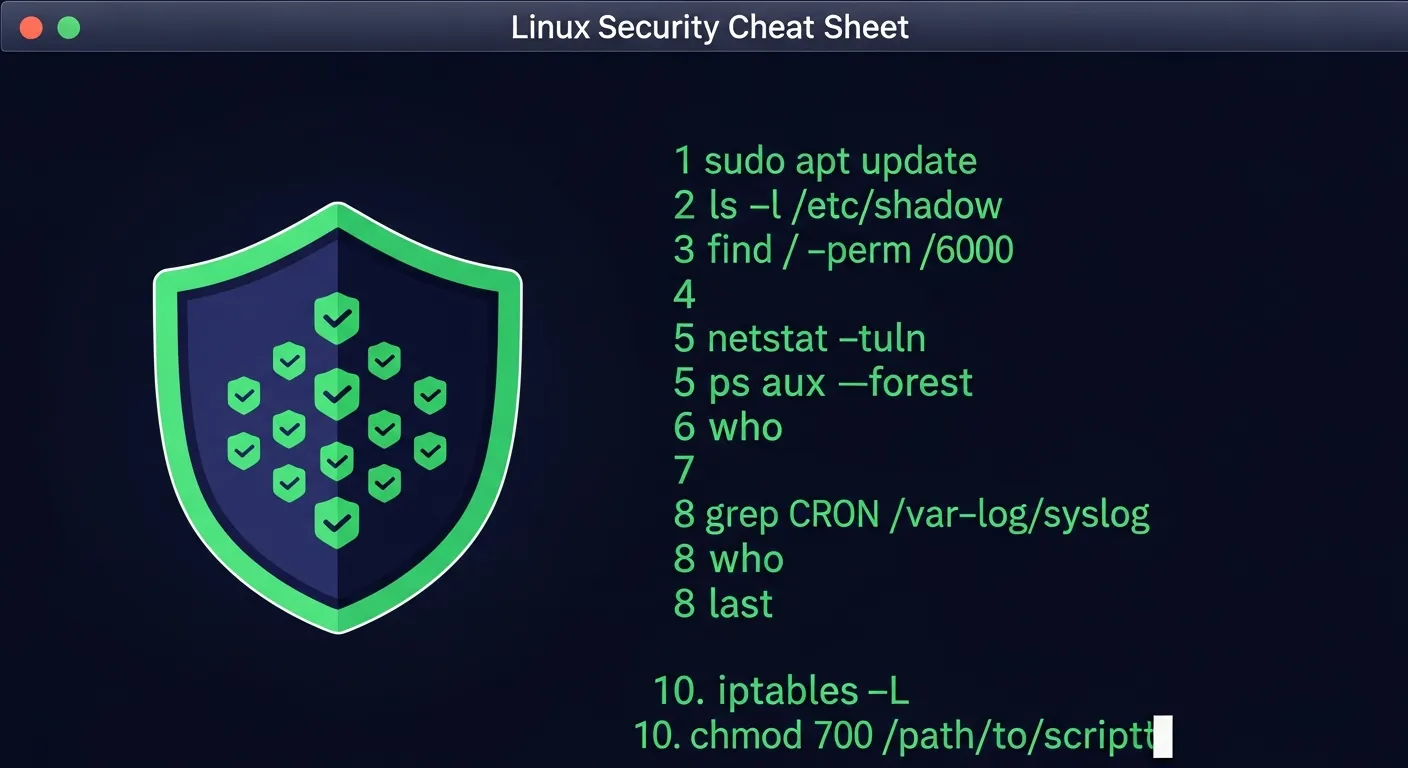
Network scanning and port discovery quick reference CCNA 200-301 Cheatsheet
Complete Cisco certification exam reference nftables Complete Guide
Linux firewall configuration and packet filtering Cybersecurity Complete Guide
Comprehensive security framework and best practices
Master networking from the ground up 📦 Cybersecurity Career Bundle
Everything you need to start a cybersecurity career 📋 All 204 Cheat Sheets
Browse our complete collection of free IT cheat sheets 📝 204 Free IT Cheat Sheets 2026
The ultimate collection guide
Stay Updated with IT Insights
Get new cheat sheets, guides, and exclusive deals delivered to your inbox.
Subscribe to Newsletter →