A firewall is only as good as its configuration. Misconfigured firewall rules are one of the most common security findings in penetration tests — overly permissive rules that allow all traffic, database ports open to the world, and missing default deny policies leave servers exposed to attacks that should be blocked.
dargslan-firewall-audit automates the tedious process of reviewing firewall rules by parsing iptables, nftables, and UFW configurations, detecting common misconfigurations, and reporting actionable security issues.
Installing dargslan-firewall-audit
pip install dargslan-firewall-audit
# Or install the complete 15-tool toolkit
pip install dargslan-toolkitCLI Usage
# Full firewall audit report
dargslan-fwaudit report
# List all rules
dargslan-fwaudit rules
# Show security issues only
dargslan-fwaudit issues
# Show chain summaries
dargslan-fwaudit chains
# Detect firewall type
dargslan-fwaudit type
# JSON output
dargslan-fwaudit jsonPython API
from dargslan_firewall_audit import FirewallAudit
fa = FirewallAudit()
# Full report
fa.print_report()
# Detect active firewall
fw_type = fa.detect_firewall()
print(f"Firewall type: {fw_type}") # iptables, nftables, or ufw
# Get all rules
rules = fa.get_rules()
for r in rules:
print(f" {r['chain']:10s} {r['action']:8s} {r['protocol']:5s} {r.get('port', '*'):>5s} {r.get('source', '*')}")
# Get chain info
chains = fa.get_chains()
for c in chains:
print(f" {c['name']:15s} Policy: {c['policy']:8s} Rules: {c['rule_count']}")
# Run audit — detect issues
issues = fa.audit()
for i in issues:
print(f" [{i['severity']:8s}] {i['message']}")
# Check specific concerns
if fa.has_default_deny():
print("OK: Default deny policy in place")
else:
print("WARNING: No default deny policy!")iptables Reference
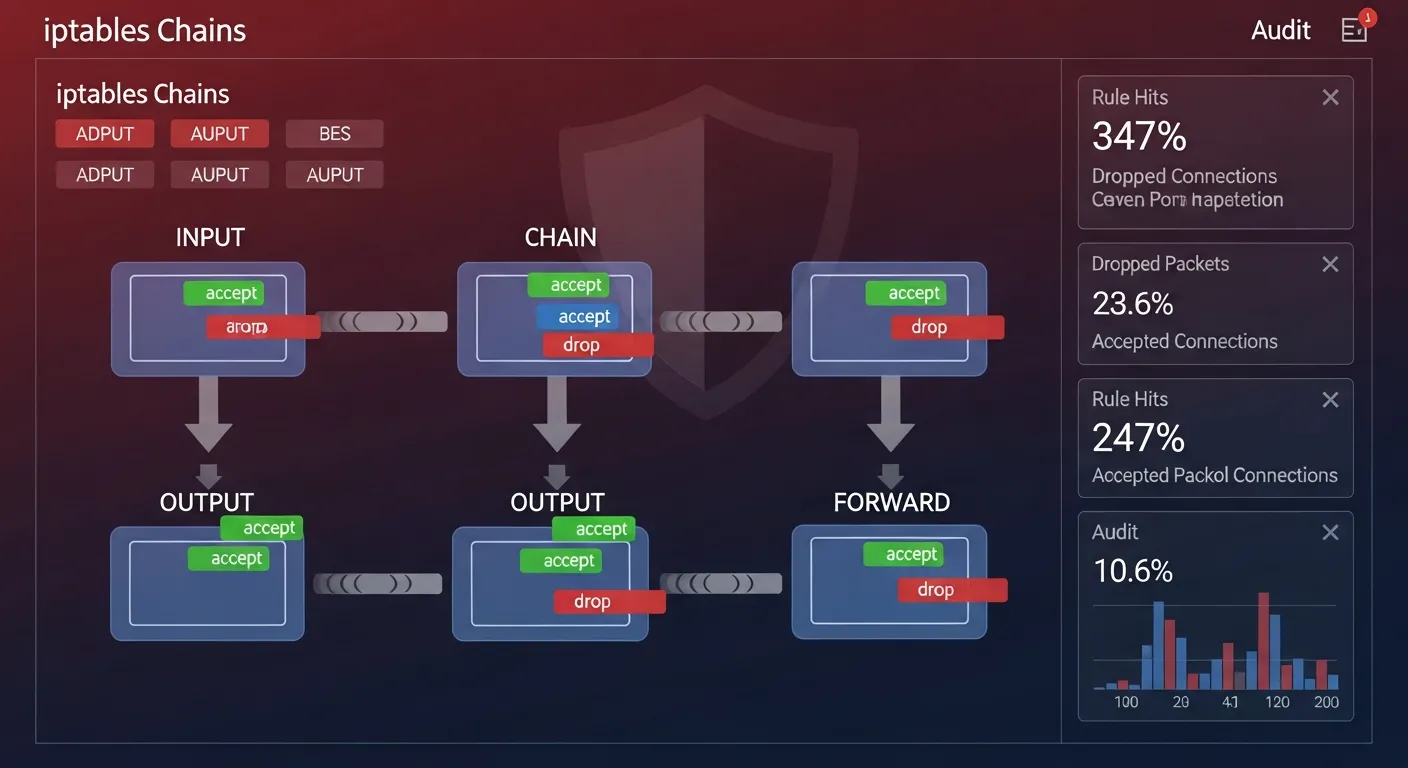
Understanding Chains
- INPUT — Traffic coming INTO the server (most important to secure)
- OUTPUT — Traffic going OUT from the server
- FORWARD — Traffic being routed through the server (routers/NAT)
Essential iptables Commands
# List all rules with line numbers
iptables -L -n -v --line-numbers
# List specific chain
iptables -L INPUT -n -v
# Set default policy to DROP
iptables -P INPUT DROP
iptables -P FORWARD DROP
iptables -P OUTPUT ACCEPT
# Allow established connections
iptables -A INPUT -m conntrack --ctstate ESTABLISHED,RELATED -j ACCEPT
# Allow loopback
iptables -A INPUT -i lo -j ACCEPT
# Allow SSH
iptables -A INPUT -p tcp --dport 22 -j ACCEPT
# Allow HTTP/HTTPS
iptables -A INPUT -p tcp --dport 80 -j ACCEPT
iptables -A INPUT -p tcp --dport 443 -j ACCEPT
# Block specific IP
iptables -A INPUT -s 203.0.113.0/24 -j DROP
# Rate limit SSH
iptables -A INPUT -p tcp --dport 22 -m conntrack --ctstate NEW -m limit --limit 3/min --limit-burst 3 -j ACCEPT
# Save rules (Debian/Ubuntu)
iptables-save > /etc/iptables/rules.v4
# Restore rules
iptables-restore < /etc/iptables/rules.v4nftables Reference (Modern Replacement)
# List all rules
nft list ruleset
# Create basic firewall
nft add table inet filter
nft add chain inet filter input { type filter hook input priority 0 \; policy drop \; }
nft add chain inet filter forward { type filter hook forward priority 0 \; policy drop \; }
nft add chain inet filter output { type filter hook output priority 0 \; policy accept \; }
# Allow established
nft add rule inet filter input ct state established,related accept
# Allow loopback
nft add rule inet filter input iif lo accept
# Allow SSH, HTTP, HTTPS
nft add rule inet filter input tcp dport { 22, 80, 443 } accept
# Save
nft list ruleset > /etc/nftables.confUFW (Uncomplicated Firewall)
# Enable/check status
ufw enable
ufw status verbose
# Default policies
ufw default deny incoming
ufw default allow outgoing
# Allow services
ufw allow 22/tcp
ufw allow 80/tcp
ufw allow 443/tcp
ufw allow from 10.0.0.0/8 to any port 5432
# Deny specific
ufw deny 3306/tcp
ufw deny from 203.0.113.0/24
# Rate limiting
ufw limit ssh
# Delete rule
ufw delete allow 8080/tcpCommon Firewall Security Issues
- No default deny policy — INPUT chain set to ACCEPT, allowing all traffic by default
- Database ports exposed — 3306, 5432, 6379 accessible from 0.0.0.0/0
- FORWARD chain open — Allows traffic routing even when server is not a router
- No rate limiting — SSH and other services vulnerable to brute force
- Rules not persistent — Firewall rules lost after reboot
- Overly broad rules — Allowing all ports from all sources
- ICMP completely blocked — Breaks MTU discovery and diagnostics
Automated Firewall Audit
#!/usr/bin/env python3
# /opt/scripts/firewall-check.py
from dargslan_firewall_audit import FirewallAudit
fa = FirewallAudit()
issues = fa.audit()
critical = [i for i in issues if i['severity'] == 'critical']
high = [i for i in issues if i['severity'] == 'high']
if critical:
print(f"CRITICAL: {len(critical)} critical firewall issues!")
for i in critical:
print(f" ! {i['message']}")
if high:
print(f"WARNING: {len(high)} high severity firewall issues")
if not fa.has_default_deny():
print("CRITICAL: No default deny policy on INPUT chain!")🔥 Master Linux Firewall Configuration
Our cybersecurity eBooks cover iptables, nftables, UFW, firewalld, advanced rule design, and enterprise firewall architecture.
Browse Security Books →Firewall misconfiguration is one of the top causes of security breaches. dargslan-firewall-audit automates the review of iptables, nftables, and UFW rules — detecting missing default deny policies, exposed database ports, and overly permissive configurations.
Install now: pip install dargslan-firewall-audit — or get all 15 tools: pip install dargslan-toolkit
Download our free Firewall Audit Cheat Sheet for quick reference.