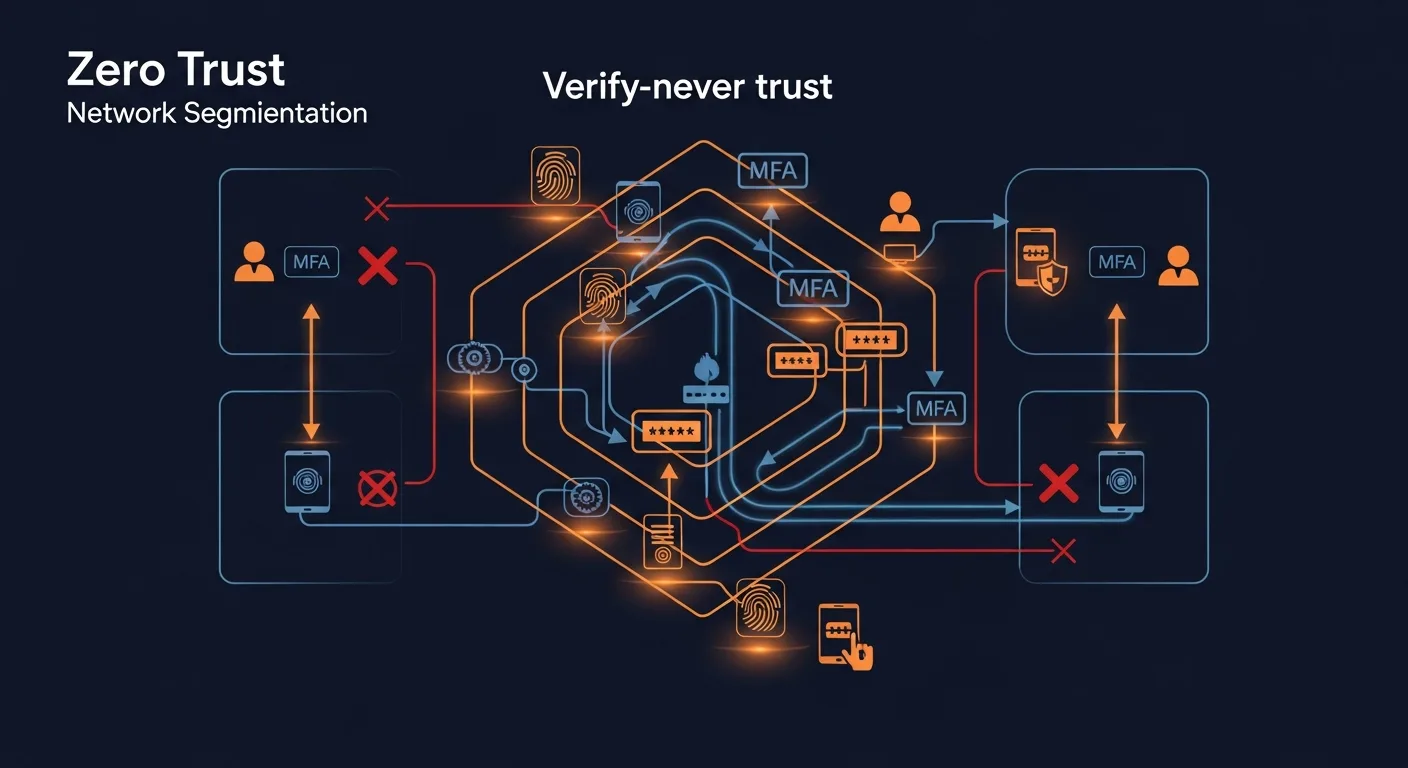
Zero Trust is not a product you can buy — it is a security architecture and philosophy that fundamentally changes how organizations think about network security. Instead of trusting users and devices inside the corporate network, Zero Trust requires continuous verification of every access request, regardless of where it originates.
📥 Free Cloud Security Framework Cheat Sheet
Includes Zero Trust maturity model, implementation roadmap, and framework cross-reference.
Download Free PDF →Table of Contents
- What is Zero Trust?
- Core Principles
- The Five Pillars
- Maturity Model
- Zero Trust vs Traditional Security
- Key Technologies
- Implementation Roadmap
- Common Challenges
- Zero Trust in the Cloud
- Best Practices
What is Zero Trust?
Zero Trust was first conceptualized by John Kindervag at Forrester Research in 2010. The core idea is simple but revolutionary: never trust, always verify. Traditional security models operate on the assumption that everything inside the corporate network can be trusted. Zero Trust eliminates this implicit trust entirely.
In a Zero Trust architecture:
- Every access request is fully authenticated, authorized, and encrypted before granting access
- Access is granted based on all available data points: identity, device health, location, resource sensitivity, and anomaly detection
- Access is limited to the minimum required (least privilege)
- The system assumes breach has already occurred and minimizes blast radius
The shift from "trust but verify" to "never trust, always verify" reflects the reality of modern IT: there is no network perimeter. With cloud services, remote workers, mobile devices, and IoT, the traditional castle-and-moat approach to security is obsolete.
Core Principles
1. Verify Explicitly
Authenticate and authorize based on all available data points. This includes user identity, device health, location, service/workload, data classification, and anomalies. Multi-factor authentication (MFA) is the foundation, but true Zero Trust goes beyond MFA to continuous, risk-adaptive authentication.
2. Use Least Privilege Access
Limit user access with Just-In-Time (JIT) and Just-Enough-Access (JEA) policies. Users get the minimum permissions needed, for the minimum time required. This reduces the impact of compromised credentials and limits lateral movement.
3. Assume Breach
Operate as if your network is already compromised. Minimize blast radius and segment access. Verify end-to-end encryption, use analytics to detect anomalies, and drive threat detection and improvements.
The Five Pillars of Zero Trust
| Pillar | Focus | Key Technologies | Quick Wins |
|---|---|---|---|
| Identity | Who is requesting access? | MFA, SSO, IdP, PAM, RBAC | Deploy MFA everywhere |
| Device | Is the device trustworthy? | MDM, EDR, compliance checks | Require device compliance |
| Network | Micro-segmentation | ZTNA, SDP, firewalls, DNS | Replace VPN with ZTNA |
| Application | App-level controls | CASB, WAF, API gateway | Shadow IT discovery |
| Data | Protect the actual data | DLP, classification, encryption | Classify sensitive data |
Zero Trust Maturity Model
The CISA Zero Trust Maturity Model defines four levels of maturity across each pillar:
| Level | Identity | Network | Data |
|---|---|---|---|
| Traditional | Passwords only | Perimeter firewall, VPN | No classification |
| Initial | MFA for some users | Some segmentation | Basic DLP policies |
| Advanced | MFA everywhere, SSO | Micro-segmentation | Automated classification |
| Optimal | Continuous, risk-adaptive | Full ZTNA, software-defined | Real-time protection |
Zero Trust vs Traditional Security
| Aspect | Traditional (Perimeter) | Zero Trust |
|---|---|---|
| Trust model | Trust inside, block outside | Never trust, always verify |
| Network access | VPN = full network access | Per-application access only |
| Authentication | Once at the perimeter | Continuous, context-aware |
| Lateral movement | Easy (flat network) | Blocked (micro-segmentation) |
| Remote access | VPN tunnel to office | Direct, secure access from anywhere |
| Breach impact | Large (full network exposed) | Contained (minimal blast radius) |
Key Technologies
- Identity Provider (IdP) — Microsoft Entra ID, Okta, Google Workspace — centralized identity management
- MFA — Phishing-resistant MFA: FIDO2 keys, passkeys, authenticator apps
- ZTNA (Zero Trust Network Access) — Zscaler, Cloudflare Access, Tailscale — replaces VPN
- EDR (Endpoint Detection & Response) — CrowdStrike, Microsoft Defender, SentinelOne
- CASB (Cloud Access Security Broker) — Controls access to cloud applications
- SIEM/SOAR — Centralized logging, threat detection, automated response
- PAM (Privileged Access Management) — CyberArk, BeyondTrust — manages admin access
Implementation Roadmap
Phase 1: Foundation (0-6 months)
- Deploy MFA on all accounts (blocks 99.9% of account compromises)
- Implement SSO with a centralized Identity Provider
- Create complete asset and identity inventories
- Classify data by sensitivity level
Phase 2: Enhanced Controls (6-12 months)
- Deploy EDR on all endpoints
- Implement device compliance policies
- Begin network segmentation planning
- Deploy CASB for SaaS visibility
Phase 3: Advanced (12-18 months)
- Replace VPN with ZTNA for application access
- Implement micro-segmentation
- Deploy DLP policies for sensitive data
- Automate access reviews and governance
Phase 4: Optimization (18-24 months)
- Continuous authentication and risk scoring
- AI-driven anomaly detection
- Automated incident response (SOAR)
- Full data lifecycle protection
Common Challenges
- Legacy applications — Older apps may not support modern authentication. Use application proxies or identity-aware proxies
- User experience — Excessive authentication friction. Use risk-adaptive policies: more verification for sensitive resources, less for routine access
- Complexity — Zero Trust is a journey, not a destination. Start small, iterate
- Budget — Phased approach. Many Zero Trust capabilities are included in existing licenses (Microsoft E5, Google Workspace Enterprise)
- Cultural resistance — Staff may resist changes. Communicate the "why" and show productivity benefits
Zero Trust in the Cloud
Cloud environments are naturally suited for Zero Trust because they already lack a traditional perimeter. Key cloud-native Zero Trust technologies:
- AWS — IAM policies, Security Groups, VPC segmentation, AWS SSO, GuardDuty
- Azure — Entra ID Conditional Access, Azure Firewall, Microsoft Defender for Cloud
- Google Cloud — BeyondCorp Enterprise, Identity-Aware Proxy, VPC Service Controls
Best Practices
- Start with identity — MFA is the single highest-ROI security control
- Map your data flows — Understand where sensitive data lives and how it moves
- Adopt ZTNA over VPN — Per-application access is more secure and better for remote workers
- Implement least privilege — Review and reduce access regularly, use JIT access
- Monitor everything — Centralized logging and analytics are essential for detecting anomalies
- Automate responses — Use SOAR to automatically block suspicious activity
- Test continuously — Regular penetration testing validates your Zero Trust controls
📥 Download the Cloud Security Cheat Sheet
Complete framework comparison, Zero Trust maturity model, and implementation roadmap in a printable PDF.
Download Free PDF →



