Mastering nftables: A Practical Guide to Modern Linux Firewalling and Network Security
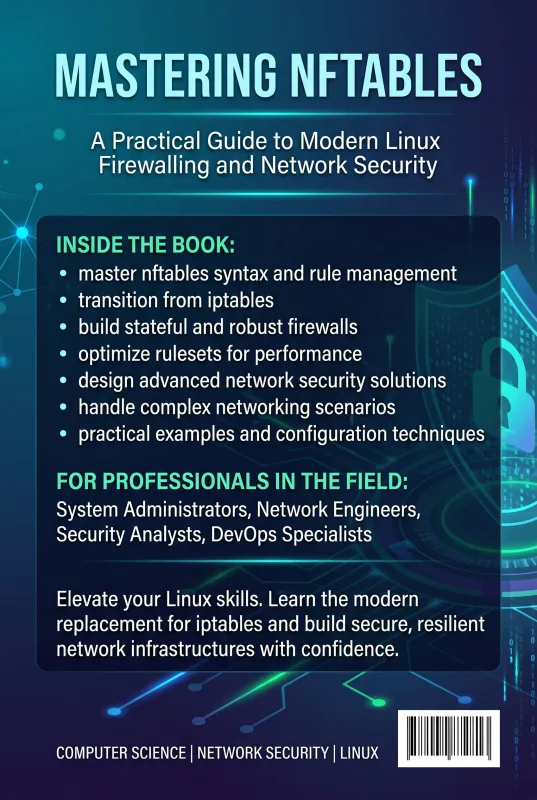
What's Included:
Key Highlights
- 20 comprehensive chapters covering every aspect of nftables — from fundamentals to production deployment
- Hands-on examples and real-world configurations you can deploy immediately
- Complete coverage of tables, chains, rules, expressions, and the nft command-line interface
- Master sets, maps, and verdict maps — the data structures that make nftables faster than iptables
- Stateful firewalling, connection tracking, and intelligent traffic decisions explained clearly
- NAT, port forwarding, and routing patterns for gateways and home networks
- Rate limiting, logging, and attack mitigation strategies for production environments
- Dedicated chapters for servers, desktops, laptops, routers, and gateways
- Practical iptables-to-nftables migration strategies with translation examples
- Automation, persistence with systemd, and professional troubleshooting techniques
- Best practices distilled from real datacenter and home lab deployments
- Distribution-agnostic — works on Debian, Ubuntu, RHEL, Fedora, Arch, and more
Overview
Master modern Linux firewalling with nftables. From your first nft command to building production-grade firewalls, gateways, and hardened servers — this hands-on guide takes you from beginner to expert with real-world examples.
The Problem
Linux firewalling has changed — but most documentation hasn't kept up. If you are still writing iptables rules in 2025, you are dealing with deprecated tooling, fragmented syntax across IPv4 and IPv6, and chains that grow unmaintainable as your infrastructure scales.
Meanwhile, nftables is now the default firewall framework on every major Linux distribution — Debian, Ubuntu, RHEL, Fedora, Arch, openSUSE — yet most administrators are stuck copying rules from outdated blog posts, fighting cryptic error messages, and never quite understanding the underlying architecture.
The result? Firewalls that are slower than they need to be, harder to audit than they should be, and impossible to scale without rewriting from scratch. That is a problem worth solving.
The Solution
Mastering nftables gives you a single, structured, professional path from your first nft command to designing production-grade firewall infrastructure with confidence.
Instead of fragmented tutorials, you get 20 progressive chapters that build mastery layer by layer — architecture first, then syntax, then practical firewalling, then advanced operations like NAT, rate limiting, logging, and automation. Every concept is reinforced with real-world configurations you can deploy immediately.
You will learn not just what to type, but why nftables works the way it does. You will master sets, maps, and verdict maps — the data structures that make nftables dramatically faster and cleaner than iptables. And you will leave with the intuition to debug, design, and harden any Linux network environment you encounter.
About This Book
Take Full Control of Linux Network Security with nftables
The Linux firewall has evolved. nftables is the modern, unified successor to iptables, ip6tables, arptables, and ebtables — and it is now the default packet filtering framework on Debian, Ubuntu, RHEL, Fedora, Arch, and virtually every major Linux distribution. Yet despite its growing adoption, most administrators still struggle with its syntax, abstractions, and full potential.
Mastering nftables changes that. This comprehensive, hands-on guide is designed to take you from your first nft command all the way to architecting production-grade firewalls, gateways, and hardened servers with confidence and precision.
Why nftables, Why Now
If you are still writing iptables rules in 2025, you are working harder than you need to. nftables offers a single unified syntax for IPv4, IPv6, ARP, and bridge filtering. It introduces powerful data structures like sets, maps, and verdict maps that make rules faster, cleaner, and easier to maintain. It supports atomic rule replacement, native scripting, and dramatically reduces the complexity of stateful firewalling.
This book is built on a simple philosophy: mastery comes from practice, context, and clarity. Every chapter blends conceptual depth with real-world examples and configurations you can adapt immediately to servers, desktops, routers, and gateways.
What Makes This Book Different
Most nftables resources are either fragmented man pages or shallow blog posts. Mastering nftables delivers something different: a structured, progressive learning path written by professionals for professionals. You will not just memorize commands — you will develop the intuition needed to design, deploy, and debug firewall infrastructure in any Linux environment.
Inside the Book
Across 20 carefully sequenced chapters, you will master:
- The architecture and philosophy of nftables — tables, chains, rules, and expressions
- The nft command-line interface, from basic syntax to advanced scripting
- Stateful firewalling, connection tracking, and intelligent traffic decisions
- Sets, maps, and verdict maps — the data structures that make nftables faster than iptables
- NAT, port forwarding, and routing for gateways and home networks
- Rate limiting, logging, and attack mitigation for production environments
- Smooth migration paths from iptables, with practical translation strategies
- Automation, persistence, and troubleshooting techniques used by professionals
Who Should Read This Book
Whether you are a system administrator securing a fleet of servers, a network engineer designing a corporate gateway, a DevOps practitioner automating infrastructure, or a security professional hardening production systems, Mastering nftables gives you the depth and clarity to do your job better.
Home lab enthusiasts, self-hosters, and Linux power users will also find this book invaluable for protecting their networks and learning a skill that pays dividends across an entire career.
Real-World, Production-Ready
This is not a theoretical book. Every concept is reinforced with practical scenarios drawn from real deployments — web servers, database hosts, VPN gateways, NAT routers, hardened laptops, and more. You will leave each chapter with configurations you can paste into /etc/nftables.conf and use immediately.
From Beginner to Mastery
The book follows a deliberate progression. Chapters 1–4 lay the foundation. Chapters 5–10 build practical firewalling skills. Chapters 11–13 cover operational excellence. Chapters 14–16 apply your skills to real environments. Chapters 17–20 complete your journey with troubleshooting, automation, iptables migration, and best practices.
Whether you read it cover to cover or use it as a reference, Mastering nftables will become the book you reach for whenever Linux networking is on the line.
Welcome aboard. Let's begin the journey toward mastering nftables together.
Who Is This Book For?
- System administrators securing servers, VPS instances, or entire fleets
- Network engineers designing gateways, routers, and segmented networks
- DevOps and SRE professionals automating firewall configuration as code
- Security professionals hardening production Linux systems
- Home lab enthusiasts and self-hosters protecting personal infrastructure
- Linux power users migrating from iptables to modern tooling
- Students and certification candidates preparing for LPIC, RHCE, or similar exams
- Anyone who wants to truly understand Linux firewalling — not just copy rules
Who Is This Book NOT For?
- Readers looking for a Windows Firewall or pfSense GUI tutorial — this book is strictly Linux and CLI-focused
- Absolute Linux beginners who have never used a terminal — basic shell familiarity is assumed
- Those seeking only a quick cheat sheet — this is a comprehensive guide, not a reference card
- Developers looking for application-layer firewalls or WAF tutorials — nftables operates at the network/transport layer
- Readers who refuse to leave iptables behind — while migration is covered, this book embraces the modern nftables approach
Table of Contents
- Introduction to nftables
- Linux Networking Fundamentals
- nftables Architecture Explained
- Getting Started with the nft Command
- Building a Basic Firewall
- Working with Ports and Services
- Address Filtering
- Stateful Firewalling
- Sets, Maps, and Verdict Maps
- NAT and Port Forwarding
- Logging and Monitoring
- Rate Limiting and Attack Protection
- Advanced Rule Matching
- Firewall Rules for Servers
- Desktop and Laptop Protection
- nftables for Routers and Gateways
- Troubleshooting nftables
- Automation and Persistence
- Migrating from iptables to nftables
- Best Practices and Next Steps
Requirements
- A running Linux system (Debian, Ubuntu, Fedora, RHEL, Arch, or any modern distribution)
- Basic familiarity with the Linux command line and shell navigation
- Root or sudo access to configure firewall rules
- A general understanding of TCP/IP networking concepts (IP addresses, ports, protocols)
- A text editor of your choice (vim, nano, VS Code, etc.)
- Optional: a virtual machine or test system to safely experiment with rules
- No prior nftables or iptables experience required — the book starts from the fundamentals