
Linux Security Auditing
Monitoring, Auditing, and Verifying the Security of Linux Systems
What's Included:
Key Highlights
- Linux-specific security auditing methodology
- Baseline and configuration verification
- auditd and kernel-level auditing
- SELinux and AppArmor audit techniques
- Firewall and network exposure auditing
- Automation-ready audit workflows
- Compliance-oriented audit reporting
Overview
A practical Linux security auditing guide covering system baselines, auditd, permissions, SELinux, AppArmor, firewall audits, automation, and compliance verification.
The Problem
Linux systems often lack consistent auditing processes, making it difficult to detect misconfigurations, verify security controls, and demonstrate compliance. Without structured audits, security issues remain hidden until incidents occur.
The Solution
This book provides a step-by-step Linux security auditing framework that helps you monitor, audit, and verify system security using Linux-native tools and repeatable methodologies.
About This Book
Comprehensive Linux Security Auditing for Modern Environments
Linux Security Auditing is a practical, Linux-focused guide for monitoring, auditing, and verifying the security of Linux systems across servers, cloud platforms, and enterprise environments. Security auditing is essential for maintaining compliance, identifying vulnerabilities, and ensuring systems remain secure over time.
This book provides a structured methodology for identifying security weaknesses, validating system configurations, and maintaining continuous audit readiness in Linux-based infrastructures.
What You Will Learn
- Defining Linux audit scope, objectives, and threat models
- Establishing secure baselines and configuration standards
- Auditing user accounts, groups, and authentication mechanisms
- Reviewing privilege levels and sudo configurations
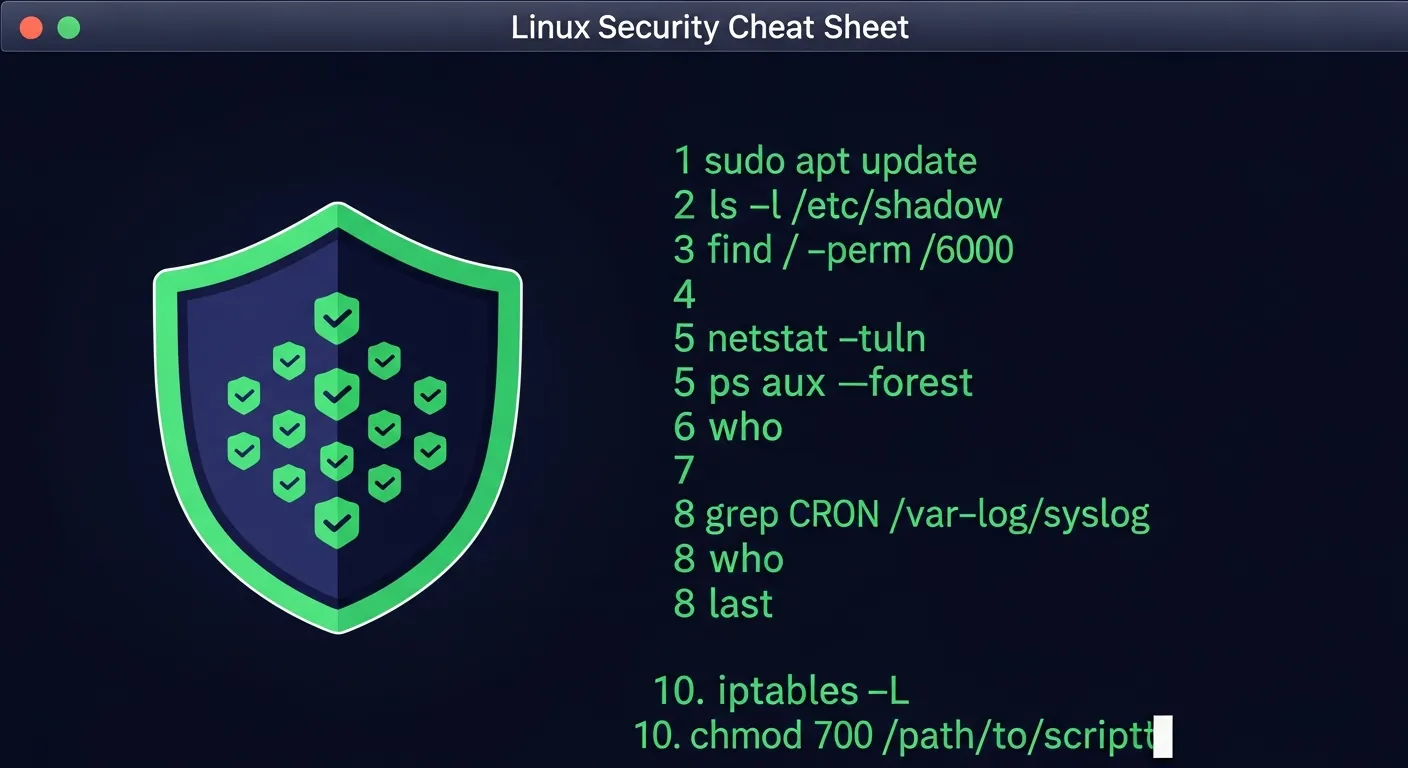
- File permission, ownership, and SUID/SGID audits
- File integrity monitoring with AIDE and similar tools
- Linux logging architecture: syslog, journald, and centralized logging
- Kernel-level auditing with auditd and audit rules
- SELinux and AppArmor policy auditing
- Firewall and network security policy reviews
- Service hardening and unnecessary service identification
- Automating security audits with scripts and tools
- Compliance mapping: CIS Benchmarks, PCI-DSS, HIPAA
- Audit reporting and remediation tracking
Who Is This Book For?
This book is designed for Linux professionals responsible for security. It is ideal for:
- Linux system administrators
- Security engineers and analysts
- Compliance officers and auditors
- DevOps engineers implementing security controls
- Anyone preparing for security certifications
Why This Book?
The book includes ready-to-use audit checklists, auditd rule examples, scripts, and compliance mappings that can be applied directly in production Linux environments.
Prerequisites
Solid Linux administration experience is required.
Author: Bas van den Berg
Who Is This Book For?
- Linux system administrators
- Security engineers and analysts
- DevOps and SRE professionals
- Compliance and audit officers
- Consultants working with Linux infrastructure
Who Is This Book NOT For?
- Absolute beginners with no Linux experience
- Readers looking for offensive hacking techniques
- High-level security theory without practical execution
Table of Contents
- What Is Linux Security Auditing
- Linux Audit Scope and Threat Models
- Establishing a Secure Baseline
- Auditing System Configuration
- User and Account Auditing
- Privilege and Access Review
- File Permission and Ownership Audits
- File Integrity Monitoring
- Linux Logging Architecture
- auditd and Kernel Auditing
- Network Exposure Auditing
- Service and Application Audits
- SELinux and AppArmor Auditing
- Firewall and Network Policy Audits
- Automating Security Audits
- Compliance and Audit Reporting
- Detecting Security Incidents via Audits
- Post-Incident Auditing
Requirements
- Basic Linux command-line experience
- Understanding of Linux system administration fundamentals
- Access to a Linux system or virtual machine