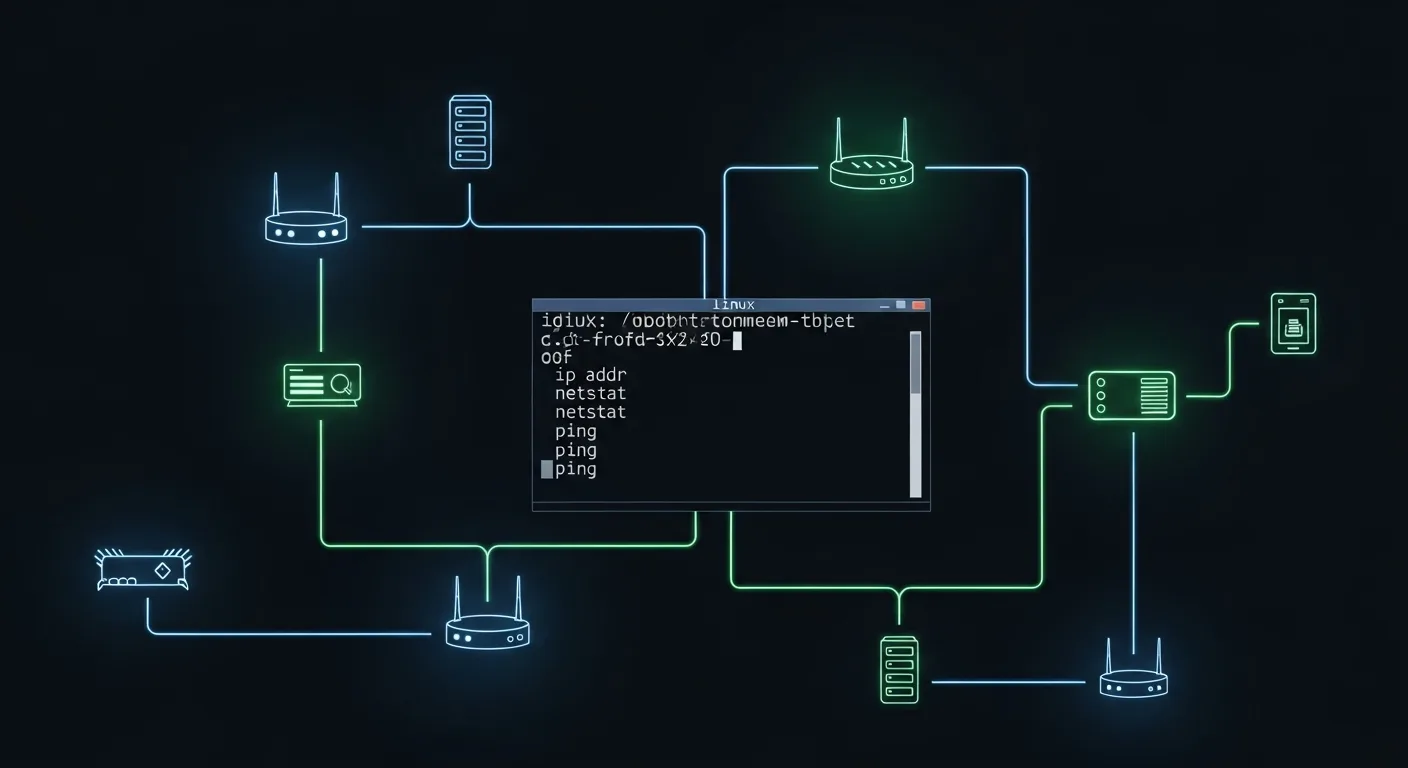
Networking is the backbone of modern IT infrastructure. Whether you're managing web servers, troubleshooting connectivity issues, or configuring firewall rules, you need a solid command of Linux networking tools. This guide covers every essential networking command you'll use as a Linux administrator, with practical, real-world examples.
📥 Free Cheat Sheet
Download our Linux Networking Commands Cheat Sheet PDF — print it, pin it, and never forget a command again.
Interface Configuration with ip
The ip command has replaced the legacy ifconfig and is the standard tool for network interface management on modern Linux distributions.
Viewing Network Interfaces
# Show all interfaces with IP addresses
ip addr show
ip a
# Show specific interface
ip addr show eth0
# Show only IPv4 addresses
ip -4 addr show
# Show brief interface summary
ip -br addr show
# Output: eth0 UP 192.168.1.100/24
# lo UP 127.0.0.1/8Managing IP Addresses
# Add an IP address
sudo ip addr add 192.168.1.200/24 dev eth0
# Remove an IP address
sudo ip addr del 192.168.1.200/24 dev eth0
# Bring interface up/down
sudo ip link set eth0 up
sudo ip link set eth0 downRouting Table Management
# Show routing table
ip route show
ip r
# Add a static route
sudo ip route add 10.0.0.0/8 via 192.168.1.1
# Add default gateway
sudo ip route add default via 192.168.1.1
# Delete a route
sudo ip route del 10.0.0.0/8Connection Analysis with ss
The ss (socket statistics) command is the modern replacement for netstat, offering faster performance and more detailed output:
# List all TCP connections
ss -t
# List all listening ports
ss -tlnp
# List all UDP sockets
ss -ulnp
# Show connections with process info
ss -tulnp
# Filter by port
ss -tlnp sport = :443
# Filter by state
ss state established
# Show connection summary
ss -sDNS Troubleshooting
dig — DNS Lookup
# Basic DNS lookup
dig example.com
# Query specific record types
dig example.com MX
dig example.com NS
dig example.com TXT
dig example.com AAAA
# Use specific DNS server
dig @8.8.8.8 example.com
# Short output
dig +short example.com
# Trace DNS resolution path
dig +trace example.com
# Reverse DNS lookup
dig -x 93.184.216.34nslookup and host
# Quick DNS lookup
nslookup example.com
host example.com
# Reverse lookup
host 93.184.216.34Connectivity Testing
ping — ICMP Echo
# Basic ping
ping example.com
# Limit count
ping -c 5 example.com
# Set interval (seconds)
ping -i 0.5 -c 10 example.com
# Set packet size
ping -s 1472 example.com
# IPv6 ping
ping6 example.comtraceroute — Path Tracing
# TCP traceroute (more reliable through firewalls)
traceroute -T example.com
# UDP traceroute (default)
traceroute example.com
# ICMP traceroute
traceroute -I example.com
# mtr — combines ping and traceroute
mtr example.com
mtr --report -c 10 example.comPacket Capture with tcpdump
The tcpdump command is indispensable for deep network troubleshooting:
# Capture on specific interface
sudo tcpdump -i eth0
# Capture specific number of packets
sudo tcpdump -i eth0 -c 100
# Filter by host
sudo tcpdump -i eth0 host 192.168.1.50
# Filter by port
sudo tcpdump -i eth0 port 443
# Filter by protocol
sudo tcpdump -i eth0 tcp
sudo tcpdump -i eth0 udp
# Save to file for analysis in Wireshark
sudo tcpdump -i eth0 -w capture.pcap
# Read from capture file
tcpdump -r capture.pcap
# Show packet contents in ASCII
sudo tcpdump -i eth0 -A port 80
# Complex filters
sudo tcpdump -i eth0 'src 192.168.1.0/24 and dst port 443'Network Scanning with nmap
# Basic port scan
nmap 192.168.1.1
# Scan specific ports
nmap -p 22,80,443 192.168.1.1
# Scan port range
nmap -p 1-1024 192.168.1.1
# Service version detection
nmap -sV 192.168.1.1
# OS detection
sudo nmap -O 192.168.1.1
# Scan entire subnet
nmap 192.168.1.0/24
# Quick scan (top 100 ports)
nmap -F 192.168.1.0/24
# Stealth SYN scan
sudo nmap -sS 192.168.1.1File Transfer Tools
curl and wget
# Download a file
curl -O https://example.com/file.tar.gz
wget https://example.com/file.tar.gz
# Follow redirects
curl -L https://example.com/redirect
# POST request with data
curl -X POST -d "user=admin&pass=secret" https://api.example.com/login
# Custom headers
curl -H "Authorization: Bearer token123" https://api.example.com/data
# Download with progress bar
curl --progress-bar -O https://example.com/large-file.isoscp and rsync
# Copy file to remote server
scp file.txt user@server:/remote/path/
# Copy directory recursively
scp -r /local/dir/ user@server:/remote/path/
# Rsync with compression and progress
rsync -avz --progress /local/dir/ user@server:/remote/dir/
# Rsync with SSH on custom port
rsync -avz -e "ssh -p 2222" /local/ user@server:/remote/Network Configuration Files
Key Configuration Files
# DNS resolver configuration
cat /etc/resolv.conf
# Hostname configuration
cat /etc/hostname
hostnamectl
# Network interfaces (Debian/Ubuntu)
cat /etc/network/interfaces
# Network Manager connections
nmcli connection show
# Hosts file
cat /etc/hostsBandwidth and Performance Testing
# iperf3 — bandwidth testing
# Server side
iperf3 -s
# Client side
iperf3 -c server-ip
# Test UDP performance
iperf3 -c server-ip -u -b 100M
# nload — real-time bandwidth monitor
nload eth0
# iftop — per-connection bandwidth
sudo iftop -i eth0
# nethogs — per-process bandwidth
sudo nethogs eth0Troubleshooting Workflow
When facing network issues, follow this systematic approach:
- Check interface status:
ip link show— Is the interface UP? - Check IP configuration:
ip addr show— Is an IP assigned? - Check routing:
ip route show— Is the default gateway set? - Check DNS:
dig example.com— Can names resolve? - Check connectivity:
ping gateway-ip→ping 8.8.8.8→ping example.com - Check services:
ss -tlnp— Is the service listening? - Check firewall:
iptables -L -nornft list ruleset - Deep inspection:
tcpdump -i eth0 port 80
📚 Go Deeper with Networking
Master Linux networking with these resources:
- Linux Networking Fundamentals — From basics to advanced routing
- Linux Networking — Deep Dive — Advanced networking for production environments
- Linux IPv6: The Complete Guide — Future-proof your network skills
- DNS Server with BIND on Linux — Build and manage DNS infrastructure




