Every open port on your Linux server is a potential entry point for attackers. Knowing exactly which ports are listening, which services are binding to all interfaces, and whether any unexpected processes have opened network connections is critical for security.
This guide covers comprehensive port monitoring using dargslan-port-monitor, a free Python tool that reads from ss, /proc/net, and provides actionable security insights about your server's network exposure.
Why Port Monitoring Is Critical
Every security audit starts with a port scan. If you don't know what ports are open on your servers, attackers will find out for you. Common issues include:
- Database ports exposed — MySQL (3306), PostgreSQL (5432), Redis (6379) accessible from the internet
- Debug services running — Development servers left running on production
- Backdoors — Compromised services listening on unusual ports
- Misconfigured services — Services binding to 0.0.0.0 instead of 127.0.0.1
Installing dargslan-port-monitor
pip install dargslan-port-monitor
# Or install the complete toolkit
pip install dargslan-toolkitCLI Usage
# Full port report with process info
dargslan-ports report
# TCP listening ports
dargslan-ports tcp
# UDP listening ports
dargslan-ports udp
# Show externally exposed ports (security focus)
dargslan-ports exposed
# Check if specific port is open on a host
dargslan-ports check 192.168.1.1 22
# JSON output
dargslan-ports jsonPython API
from dargslan_port_monitor import PortMonitor
pm = PortMonitor()
# Full port report
pm.print_report()
# Get all TCP listening ports
tcp_ports = pm.get_listening_ports()
for p in sorted(tcp_ports, key=lambda x: x['port']):
exposed = "EXPOSED" if p['exposed'] else "local"
svc = f" ({p['service']})" if p['service'] else ""
print(f" [{exposed}] {p['address']}:{p['port']}{svc}")
# Find externally exposed ports (biggest security risk)
exposed = pm.find_exposed()
for p in exposed:
print(f" WARNING: Port {p['port']} exposed on all interfaces")
# Find unexpected ports
unexpected = pm.find_unexpected(expected_ports=[22, 80, 443])
if unexpected:
print(f"ALERT: {len(unexpected)} unexpected exposed ports!")
# Check specific port
result = pm.check_port("192.168.1.1", 22)
print(f"Port 22: {'OPEN' if result['open'] else 'CLOSED'}")Linux Port Monitoring Commands
ss (Modern Tool — Recommended)
# TCP listening ports with process info
ss -tlnp
# UDP listening ports
ss -ulnp
# All connections (established + listening)
ss -tnp
# Summary statistics
ss -s
# Filter by port
ss -tlnp sport eq :80
# Filter by state
ss -tn state establishednetstat (Legacy — Still Useful)
# TCP listening
netstat -tlnp
# All connections
netstat -anp
# Statistics
netstat -sWell-Known Port Reference
| Port | Service | Should Be Exposed? |
|---|---|---|
| 22 | SSH | Yes (with key-only auth) |
| 80 | HTTP | Yes (redirect to HTTPS) |
| 443 | HTTPS | Yes |
| 3306 | MySQL | No — bind to 127.0.0.1 |
| 5432 | PostgreSQL | No — bind to 127.0.0.1 |
| 6379 | Redis | No — bind to 127.0.0.1 |
| 9090 | Prometheus | No — internal only |
Securing Exposed Ports
# Bind service to localhost only
# MySQL: /etc/mysql/mysql.conf.d/mysqld.cnf
bind-address = 127.0.0.1
# PostgreSQL: /etc/postgresql/14/main/postgresql.conf
listen_addresses = 'localhost'
# Redis: /etc/redis/redis.conf
bind 127.0.0.1
# Close port with UFW firewall
ufw deny 3306
ufw deny 5432
ufw deny 6379
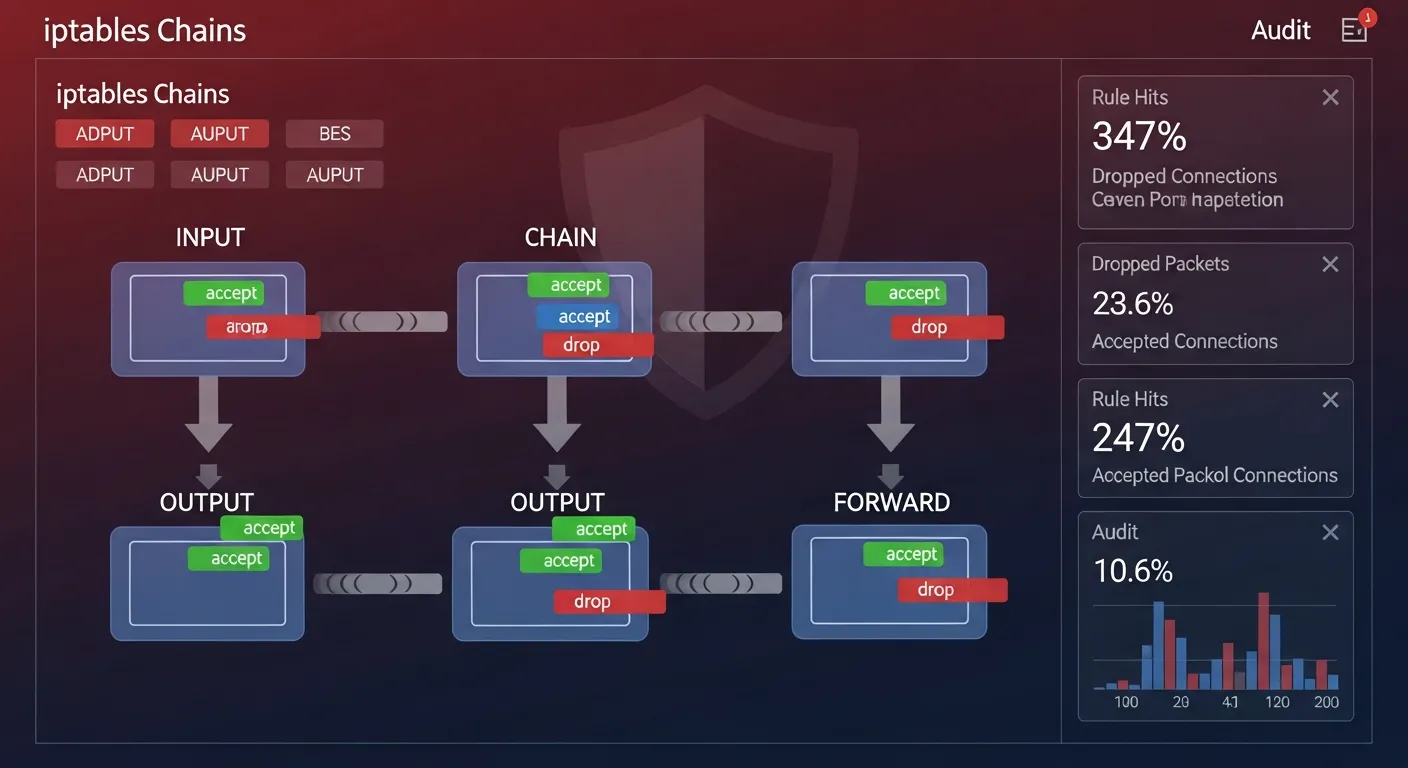
# Close port with iptables
iptables -A INPUT -p tcp --dport 3306 -j DROPAutomated Port Monitoring
#!/usr/bin/env python3
# /opt/scripts/port-check.py
from dargslan_port_monitor import PortMonitor
EXPECTED_PORTS = [22, 80, 443]
pm = PortMonitor()
# Find unexpected exposed ports
unexpected = pm.find_unexpected(expected_ports=EXPECTED_PORTS)
if unexpected:
print(f"SECURITY ALERT: {len(unexpected)} unexpected exposed ports!")
for p in unexpected:
svc = f" ({p['service']})" if p['service'] else ""
print(f" Port {p['port']}{svc} - {p['address']}")
# Monitor all exposed ports
exposed = pm.find_exposed()
print(f"\nExposed ports ({len(exposed)}):")
for p in sorted(exposed, key=lambda x: x['port']):
print(f" :{p['port']} {p.get('service', '')}")🛡️ Master Network Security
Our cybersecurity eBooks cover network security, firewall configuration, intrusion detection, port hardening, and penetration testing techniques.
Browse Security Books →Port monitoring is your first line of defense against network-based attacks. dargslan-port-monitor makes it simple to track open ports, detect exposed services, and identify security risks — without installing network scanning tools.
Install now: pip install dargslan-port-monitor — or get all 15 tools: pip install dargslan-toolkit
Download our free Port Monitor Cheat Sheet for quick reference.