The cybersecurity landscape in 2026 is more complex and dangerous than ever. AI-powered attacks, sophisticated ransomware, supply chain compromises, and an ever-expanding attack surface mean that organizations must stay ahead of threats — or face devastating consequences.
We have put together a comprehensive 12-page Cybersecurity Essentials 2026 guide covering everything from the latest threat landscape to actionable hardening checklists, compliance frameworks, and tool recommendations.

The 2026 Threat Landscape
Understanding what you are up against is the first step. Here are the most critical threats facing organizations in 2026:
- Ransomware Evolution: Triple extortion is now standard — attackers encrypt your data, steal it, and threaten DDoS attacks if you do not pay. Ransomware-as-a-Service kits are available for as little as $50.
- AI-Powered Attacks: Deepfake voice phishing, AI-generated malware that adapts in real-time, and automated reconnaissance tools are making attacks faster and harder to detect.
- Supply Chain Attacks: From compromised npm packages to CI/CD pipeline breaches, attackers are targeting the software supply chain to reach thousands of organizations at once.
- Cloud Misconfigurations: Remain the #1 cause of cloud breaches. Exposed S3 buckets, over-privileged IAM roles, and unencrypted storage continue to be low-hanging fruit for attackers.
- Identity-Based Attacks: Credential stuffing, MFA fatigue attacks, and session hijacking are increasingly sophisticated.
Key statistic: The average cost of a data breach has risen to $4.88 million, and it takes organizations an average of 194 days to even identify a breach.
Zero Trust: The New Security Standard
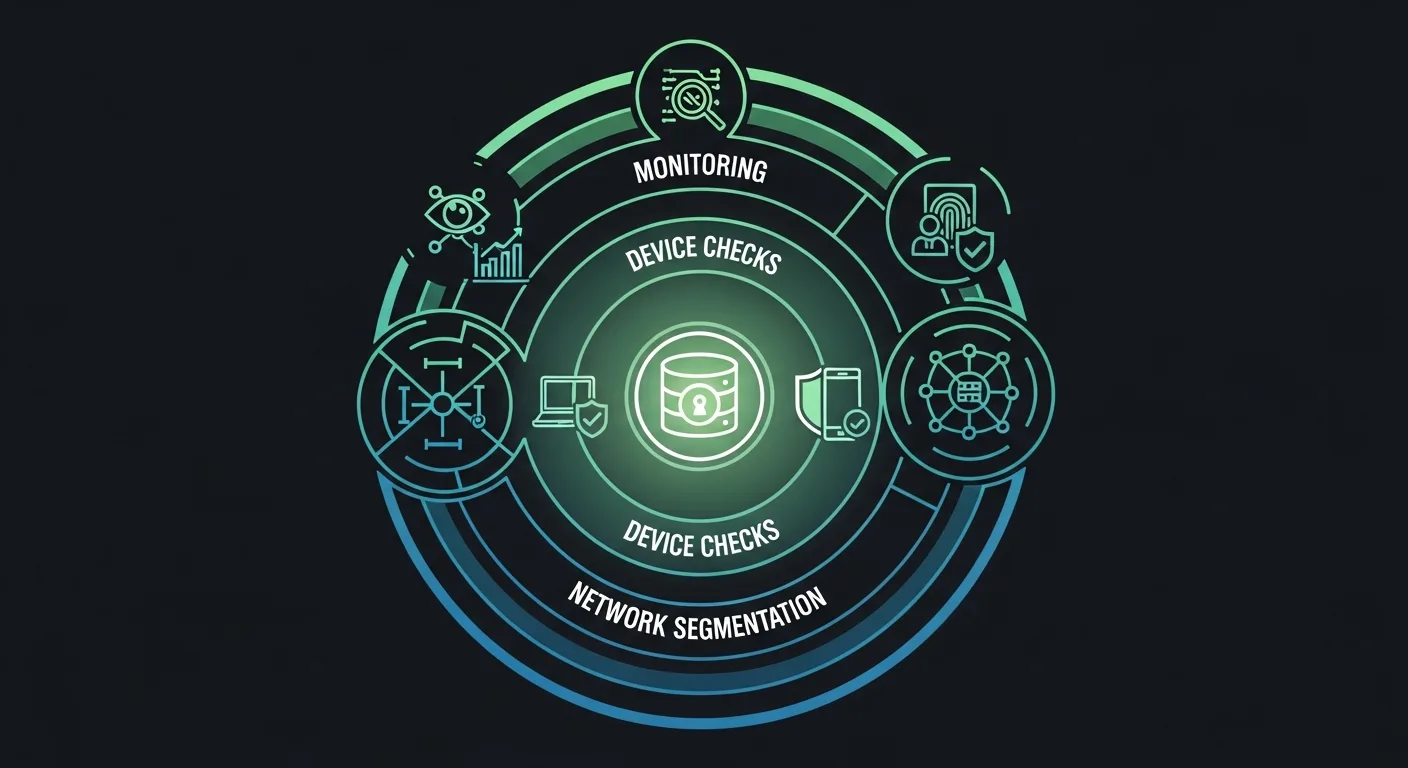
Zero Trust Architecture has moved from buzzword to necessity. The core principle is simple: "Never trust, always verify." Every access request must be authenticated, authorized, and continuously validated — regardless of where it comes from.
The Zero Trust implementation path:
- Start with Identity: Deploy phishing-resistant MFA for all users (FIDO2/WebAuthn)
- Implement Least Privilege: RBAC/ABAC with just-in-time access provisioning
- Micro-segment Networks: Isolate workloads, control east-west traffic
- Deploy EDR: Endpoint Detection and Response on all devices
- Continuous Monitoring: Real-time risk scoring and adaptive access policies
Our cheat sheet includes a complete 10-item Zero Trust implementation checklist with priority levels.
Cloud Security in 2026
With most organizations now running multi-cloud environments, securing cloud infrastructure requires a structured approach:
- AWS: IAM policies with least privilege, S3 Block Public Access, CloudTrail in all regions, GuardDuty enabled
- Azure: Conditional Access policies, Azure Security Center, Activity Log monitoring
- GCP: Organization policies, VPC Service Controls, Cloud Armor
The guide covers 8 AWS-specific security best practices and a multi-cloud security checklist applicable to all providers.
Linux Server Hardening
For those running production Linux servers, our guide includes a 15-point hardening checklist with specific commands:
- SSH hardening (key-only auth, custom ports, Ed25519 keys)
- Firewall configuration with nftables
- Automatic security updates
- SELinux/AppArmor enforcement
- Audit logging with auditctl
- Kernel hardening via sysctl
- File integrity monitoring (AIDE/Tripwire)
- Fail2ban brute force protection
Plus complete sysctl security settings you can copy directly to your servers.
Security Monitoring and SIEM

You cannot protect what you cannot see. Our guide compares 8 SIEM platforms (including free options like Wazuh and Elastic SIEM) and identifies the 7 critical log sources every organization should monitor:
- Authentication logs (failed logins, brute force, MFA bypass)
- Firewall logs (blocked connections, port scans)
- Web server logs (injection attempts, path traversal)
- DNS logs (C2 beacons, DNS tunneling)
- Cloud audit logs (IAM changes, resource creation)
- Endpoint logs (process creation, file modifications)
- Email logs (phishing attempts, SPF/DKIM failures)
AI in Cybersecurity: Double-Edged Sword

AI is transforming cybersecurity on both sides of the battlefield:
AI Threats to Watch:
- Deepfake phishing (AI-generated voice/video impersonation)
- Polymorphic AI malware that adapts to evade detection
- Prompt injection attacks against LLM-powered applications
- ML-optimized password cracking (PassGAN)
- Data poisoning of AI training sets
AI Defenses to Deploy:
- User and Entity Behavior Analytics (UEBA)
- AI-powered threat detection for zero-day attacks
- Security Orchestration, Automation, and Response (SOAR)
- NLP-based phishing detection
- AI-managed honeypots and deception technology
What Else Is Inside?
The complete 12-page PDF also covers:
- Encryption Standards 2026: AES-256-GCM, Ed25519, TLS 1.3, Argon2id, and post-quantum readiness (CRYSTALS-Kyber)
- Incident Response Framework: NIST 6-phase lifecycle with a "First 60 Minutes" checklist and evidence collection commands
- OWASP Top 10: Complete mitigation guide for each vulnerability plus essential security headers
- Compliance Frameworks: NIST CSF 2.0, ISO 27001, SOC 2, PCI DSS v4.0, GDPR, HIPAA, NIS2, DORA
- 20+ Security Tools: Organized by category — vulnerability scanning, penetration testing, and defense/monitoring
- Certification Roadmap: From CompTIA Security+ to CISSP, with salary impact data
Download the Cybersecurity Essentials 2026 Guide
The complete 12-page PDF is free to download.
Download Cybersecurity Essentials 2026 PDF (Free) →
Recommended Reading
Deepen your cybersecurity knowledge with these books from our collection:
- Mastering Kali Linux: Penetration Testing and Cybersecurity
- Cybersecurity Fundamentals
- Linux Security Hardening
- Ethical Hacking and Penetration Testing
- Linux Intrusion Detection with OSSEC and Wazuh
- Network Security Fundamentals
Stay secure. Bookmark this page, share it with your team, and download the free PDF. For more free cheat sheets and guides, visit our Cheat Sheets Library.